CVE-2026-3854: What GitHub’s Git Push RCE Teaches Us About Internal Trust Boundaries
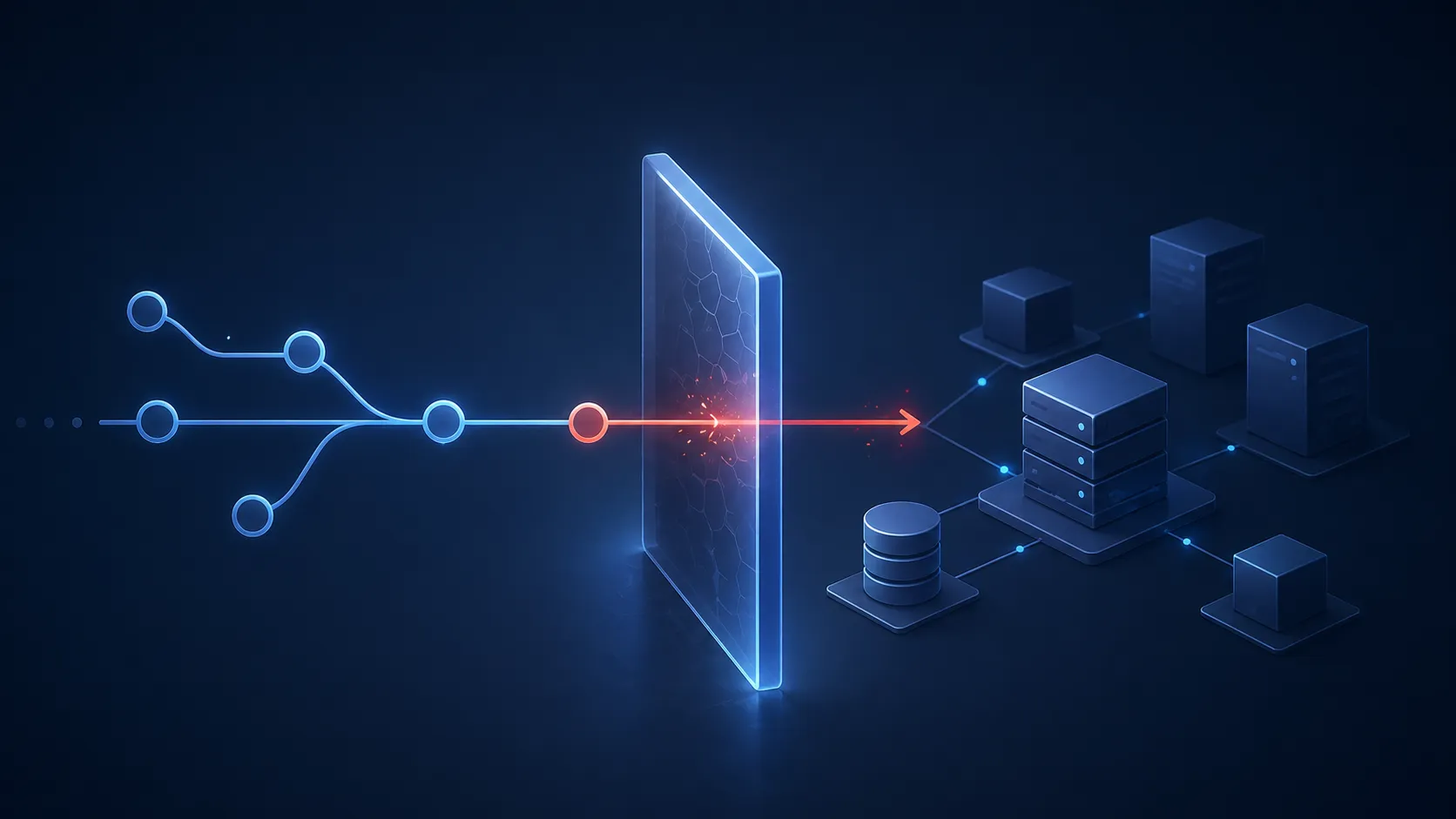
A practical security design lesson from GitHub’s git push pipeline vulnerability: authenticated workflows and internal headers do not automatically make user-controlled data safe.
Read More →
How an Ecommerce Store Could Lose $60,000 to a Single XSS Flaw
See how one browser-side XSS flaw can turn into checkout disruption, customer trust damage, incident response cost, and ecommerce revenue loss.
Read More →
Your Clean Scan Report Might Be Your Biggest Security Risk
A clean vulnerability scan does not prove your product is secure. Learn why scanners miss business logic flaws, API authorization issues, and real attack paths.
Read More →
OWASP Top 10 in 2026: A Practical Prioritization Guide for Small Teams
Small teams should not fix security issues by checklist order alone. Learn how to prioritize OWASP risks by exposure, exploitability, and business impact.
Read More →
Why WordPress Sites Still Get Compromised in 2026: The Plugin Problem Behind the Headlines
Modern WordPress sites are application stacks, not simple websites. See how plugin sprawl, admin risk, and unmanaged exposure still lead to compromise.
Read More →
AWS Misconfiguration Is Still the Fastest Way to Turn a Small Mistake Into a Big Incident
AWS incidents often begin with small misconfigurations. Learn how exposed services, weak IAM, metadata access, and storage mistakes can chain into compromise.
Read More →